You may have heard about a security issue with a very popular file called timthumb.php used by many themes and a few plugins I might add to dynamically resize images on the fly. A post about it is here – http://wpcandy.com/reports/timthumb-security-vulnerability-discovered
You may have heard about a security issue with a very popular file called timthumb.php used by many themes and a few plugins I might add to dynamically resize images on the fly. A post about it is here – http://wpcandy.com/reports/timthumb-security-vulnerability-discovered
It sounds scary but is quite easy to fix if you follow the steps in the solution section below.
Firstly check your website for malware now
Option 1: http://sitecheck.sucuri.net/scanner/
Option 2: http://safeweb.norton.com/
If you have malware stay on the website that scanned your site and use their solution as nothing on this page will fix your issue this post is about prevention before the hackers arrive. Once they are in the back door closing the door is too late. Your site will then be compromised and will need some serious effort to clean up.
What the threat means:
John Ford of Vaultpress / Automattic explains the issue and options here – http://blog.vaultpress.com/2011/08/02/vulnerability-found-in-timthumb/. John describes the potential risk as follows:
It allows third parties to upload and execute arbitrary PHP code in the TimThumb cache directory.
They tried to hack my website:
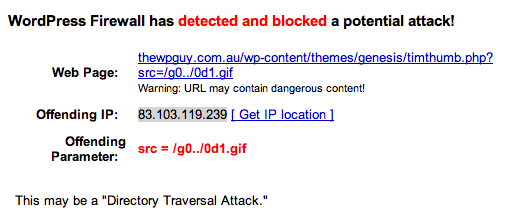
Even though I don’t even have timthumbs on my website they came looking for it. A great example of why a plugin called WordPress Firewal 2 is worth having. It blocked the hacker before they could try anything and emailed me the above message.
What is affected:
WordPress Themes:
Elegantthemes.com (older versions only) – location: themename/timthumb.php and also in epanel/timthumb.php
Woothemes.com – location themename/timbthumb.php or themename/thumb.php – there are a few great posts just for woothemes
1. www.woothemes.com/2011/08/timthumb-security-flaw-patch/
2. http://wptheming.com/2011/08/cleaning-up-the-timthumb-hack/
aqua-blue
backstage
bueno
busybee
canvas
cinch
cityguide
coffeebreak
dailyedition
deep-blue
delegate
delicate
digitalfarm
ElegantEstate
flashnews
freshnews
gazette
headlines
magazinum
Magnificent
mymag
mystream
nomadic
object
openair
optimize
overeasy
premiumnews
retreat
royalle
slanted
sophisticatedfolio
sportpress
thejournal
thestation
TheStyle
wp-creativix
WordPress Plugins:
YD recent posts widget – location: timthumb/timthumb.php
Event espresso – location: includes/functions/timthumb.php
WPTap – location: include/timthumb.php
WordPress popular posts – location: scripts/timthumb.php
a-gallery
dukapress
front-slider
geotag
highlighter
igit-posts-slider-widget
igit-related-posts-with-thumb-images-after-posts
islidex
jquery-slider-for-featured-content
kc-related-posts-by-category
lisl-last-image-slider
meenews
meenews-newsletter
mobile-smart
seo-image-galleries
shortcodes-ultimate
smart-related-posts-thumbnails
webphysiology-portfolio
wordpress-gallery-plugin
wp-mobile-detector
wp-slick-slider
shortcodes-ultimate
social-profiles-widget
woo-tumblog
There are others but I haven’t examined them first hand as yet
What to do if you haven’t been hacked yet :
Act quickly as more sites are being hacked every day and its far easier to do this process than get your site back online after being hacked and your hosting company disables the website until its cleaned.
Option 1 (one plugin does all the work for you)
Install plugin called Timthumb Vulnerability Scanner .
http://wordpress.org/extend/plugins/timthumb-vulnerability-scanner/
Go to the left hand side of your admin area -> Tools -> Timthumb Scanner ->
Click on scan button to run a scan, it takes under a minute or less usually depending on the size of your website.
Then it will show where any copies of the files exist and if they need updating.
Click Fix button to replace them with the latest safer version.
Option 2 (manual version)
Step 1: download the latest version of timthumb.php here – http://code.google.com/p/timthumb/
Step 2:
Add this line if it is not already there
define( 'ALLOW_EXTERNAL', false );
Step 3: Change this code by removing the external links
$allowedSites = array ( 'flickr.com', 'picasa.com', 'img.youtube.com', 'upload.wikimedia.org', );
To look like this ( removes all links to external sites )
$allowedSites = array();
Step 4
Save the new version and upload via ftp to replace old version in theme or plugin.
What to do if your website has already been hacked:
Pay $90 for a 1 year subscription to http://sitecheck.sucuri.net/ and get them to clean the website. And you get protected for another year as a bonus.